
With the Georgia runoff election in full swing, this article will show why the ballot results should be ash-canned even before the final tallies are in -- both Georgia and Pennsylvania adhere to the federal standard for elections and because Dominion uses modems, the election provider itself is not certifiable.
Pennsylvania state certification requires that voting systems be evaluated by a federally recognized independent testing authority, or voting system test laboratory (VSTL), and certified by the U.S. Election Assistance Commission (EAC) according to federal voting system standards.
"Once you add that modem, you are de-certifying it,” Kevin Skoglund, senior technical advisor at the National Election Defense Coalition said. “It is no longer federally certified. And I don't know that all these jurisdictions are aware of that because ES&S is advertising otherwise. The three largest voting manufacturing companies — Election Systems &Software, Dominion Voting Systems and Hart InterCivic — have acknowledged they all put modems in some of their tabulators and scanners.”-NBC
What you’re going to find is the current Dominion and ES&S voting systems were designed over 22 years ago to allow and promote every type of voter fraud imaginable and the same two conspirators have been safeguarding and selling these broken systems the entire time.
From 1997 to 2003 Bob Urosevich and Barry Herron developed the art of electronic vote manipulation to such a degree; you didn’t need to hack the system to change the election results. Below is the chain of custody for the software and source code that made this possible.
The key takeaway is simple. Although what’s described below is from Diebold Election Systems, Dominion bought Diebold and this system for use. This the backbone of Dominion Voting Systems today and it gives a clear line of sight into the otherwise opaque world of election fraud in 2020.
In 2003, a research journalist named Bev Harris opened up the world of Diebold Election Systems. When Dominion Voting Systems got off the ground and became a player it was because of the purchase of Diebold properties including systems, source code, and software.
What she found was Diebold had a 'no-login needed' website that was a detailed manual of how to hack the election systems Diebold was servicing across the US. If you didn’t like the election tallies, it was a simple matter of replacing the file with one that reflected the results you wanted on this FTP site.
According to Harris, the site was set up for election workers and technicians and included hardware and software specifications, election results files, the vote-counting program itself, and "replacement files" for Diebold's GEMS vote-counting system and for the Windows software underlying the system.
The contents of these files amounted to a virtual handbook for vote-tampering: They contained diagrams of remote communications setups, passwords, encryption keys, source code, user manuals, testing protocols, and simulators, as well as files loaded with votes and voting machine software.
Diebold Elections Systems AccuVote systems use software called "GEMS," and this system is used in 37 states. The voting system works like this:
Voters vote at the precinct, running their ballot through an optical scan, or entering their vote on a touch screen.
After the polls close, poll workers transmit the votes that have been accumulated to the county office. They do this by modem.
At the county office, there is a "host computer" with a program on it called GEMS. GEMS receives the incoming votes and stores them in a vote ledger. But in the files we examined, which were created by Diebold employees and/or county officials, we learned that the Diebold program used another set of books with a copy of what is in vote ledger 1. And at the same time, it made yet a third vote ledger with another copy.
Apparently, the Elections Supervisor never sees these three sets of books. All she sees is the reports she can run: Election summary (totals, county wide) or a detail report (totals for each precinct). She has no way of knowing that her GEMS program is using multiple sets of books, because the GEMS interface draws its data from an Access database, which is hidden. And here is what is quite odd: On the programs we tested, the Election summary (totals, county wide) come from the vote ledger 2 instead of vote ledger 1, and ledger 2 can be altered so it may or may not match ledger 1.
Now, think of it like this: You want the report to add up only the actual votes. But, unbeknownst to the election supervisor, votes can be added and subtracted from vote ledger 2. Official reports come from vote ledger 2, which has been disengaged from vote ledger 1. If one asks for a detailed report for some precincts, though, the report comes from vote ledger 1. Therefore, if you keep the correct votes in vote ledger 1, a spot check of detailed precincts (even if you compare voter-verified paper ballots) will always be correct.”
Auditing
Again from Bev Harris provided all this information on a share-as-widely-as-possible basis. The audit trail is what is supposed to guarantee election security. Harris went to the same Diebold/Dominion website and downloaded a GEMS (General Election Management System) audit report.
“Note that a user by the name of "Evildoer" was added. Evildoer performed various functions, including running reports to check his vote-rigging work, but only some of his activities showed up on the audit log.
It was a simple matter to eliminate Evildoer. First, we opened the election database in Access, where we opened the audit table: Then, we deleted all the references to Evildoer and, because we noticed that the audit log never noticed when the admin closed the GEMS program before, we tidily added an entry for that.
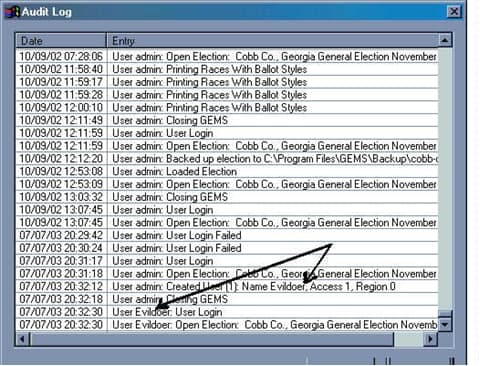
Access encourages those who create audit logs to use auto-numbering so that every logged entry has an uneditable log number. Then, if one deletes audit entries, a gap in the numbering sequence will appear. However, we found that this feature was disabled, allowing us to write in our own log numbers. We were able to add and delete from the audit without leaving a trace. Going back into GEMS, we ran another audit log to see if Evildoer had been purged:
As you can see, the audit log appears pristine.
In fact, when using Access to adjust the vote tallies we found that tampering never made it to the audit log at all.” – Bev Harris
An election (after the fact) using the real files on the real system was changed for research purposes with no elaborate hacking necessary.
The Dominion software and source code was originally developed by a company called Premier Election Solutions. The founder was Bob Urosevich.
• In 1997 Global Election Systems acquired Premier. The company representatives were Bob Urosevich and Barry Herron
• In 2001, Diebold purchased Global. The company representatives were Bob Urosevich and Barry Herron.
• In 2009, Diebold Sells U.S. Elections Systems Business to ES&S. The company representatives were Bob Urosevich and Barry Herron
• In September 2009, ES&S acquired Premier, without any objections from the DOJ. But in March 2010, the DOJ forced ES&S to “sell” Premier’s assets to Dominion. ES&S was also forced to license to Dominion some of its software for free.
• Dominion announced the acquisition of the Diebold (formerly Premier) products on May 19, 2010
• Dominion Voting Systems purchased the primary assets of Premier, including all intellectual property, software, firmware, and hardware for Premier's current and legacy optical scan, central scan, and touch screen voting systems, and all versions of the GEMS election management system from ES&S.
• Barry Herron is the Southeast regional sales manager for Dominion Voting Systems as well as being their lobbyist.
• Barry Herron is Director of sales for INTERNATIONAL LOTTERY AND TOTALIZATOR, INC.
• Barry Herron is the sales manager for Unisyn Voting. Unisyn, an HK registered company wholly owned by UNISYN VOTING SOLUTIONS (A DIVISION OF INTERNATIONAL LOTTERY AND TOTALIZATOR, INC) a division of Berjaya Lottery Management (h.k.) Ltd, a division of Yong Hong Group Co., Ltd., referred to Wing Hung Kai Group ( English: Wing Hung Kee Holdings Limited's, HKEx except when licensing 0288.HK), founded in 1971, formerly known as Wing Hung Kai Properties Limited referred to as Wing-hong Kee Property ( English: Wing Hung Kee Investment Company, Limited ). Listed on the main board of the Hong Kong Stock Exchange in 1973. In 1994, the Malaysian consortium Berjaya Group ( Berjaya Group ) acquisition, changed its name to succeed Holdings (Hong Kong) Limited.
Unisyn is a wholly-owned private corporation headquartered in Malaysia but registered in Hong Kong, China.
INTERNATIONAL LOTTERY AND TOTALIZATOR, INC is the world’s largest manufacturer of voting machine equipment.
Does Unisyn manufacture Dominion Voting Solution machines? I don’t have the answer to that but Unisyn’s Barry Herron is Dominion’s lobbyist for GA.
Along with Bob Urosevich’s ES&S, Unisyn is also one of the voting systems companies certifying the 2020 US election was the safest in history.
How important is this information? If attorneys Rudy Guliani and Sydney Powell don’t have this information yet, it will be vital in court to show the voting machine source code and system was known to be threats to national security in its previous use.
Throughout the rest of this article, I’ll be referring to "background" The Case of the Diebold FTP Site Part of the Voting and Elections web pages by Douglas W. Jones Head of THE UNIVERSITY OF IOWA Department of Computer Science. The reference will be (DWJ). His study which refers to The Johns Hopkins Study On Voting Systems (Hopkins) as well as the SAIC (Science Applications International Corp). These three reports led to the decertification of the previous iteration of Dominion’s source code and software in various states and Dr. Jones has testified before Congress on these specific issues.
I’ll also be referring to the NBC article (NBC), 'Online and vulnerable': Experts find nearly three dozen U.S. voting systems connected to internet which shows the problems the same voter software and source code used by Global Elections over 20 years ago is why Dominion Voting Systems/Diebold and ES&S/Diebold are still a national security threat today the same way they were labeled as such 17 years ago.
Lastly, How New Voting Machines Could Hack Our Democracy Jennifer Cohn for the New York Review of Books (NYRB) shows the updated methodology combined with Dominion’s source code makes election fraud easy. Comparing this to the Hopkins study or the paper by (DWG) it’s clear the level of threat election security is facing today.
At every waypoint in the election cycle from certification, planning, voting, absentee and mail-in votes, county reporting on the GEMS (General Election Management Systems), this system provides the means to monitor and change votes in real-time and even during the ballot reporting at the county level.
Throughout its history, whenever Diebold/Dominion’s source code, software, and method were inspected, it was moved under a new corporate logo.
How secure are the 2020 elections?
Using Modems for federal elections decertifies voting machines.
The state of Michigan is currently grappling with this issue. Since the 2016 election, Michigan authorized $82 million dollars to upgrade its election systems. Some of that money was spent on tabulators with wireless modems. But now, some state officials worry that the machines may pose a security risk and are pushing to have the modems removed.(NBC)
Some of the companies, agencies, groups, and people certifying the 2020 election as the safest in history represent a who’s who of people to investigate for 2020 election fraud. If one voting system company is looked at under a microscope, more of them will fall soon thereafter.
For Georgia, this means the broken Diebold system Herron replaced with new Dominion machines is the same made to be hacked system Georgia already had with a few new add-ons.
LAN and hard lines
Because hacking into the systems is easy they way Diebold/Dominion set it up, according to (DWG)’s report even the use of LAN and hard lines pose a significant security problem.
Allegation #53 (p. 16):
"Physical access to the voting results may not even be necessary to acquire the voting records if they are transmitted across the Internet."
Diebold Response:
... Results are not transmitted over the Internet.
My Added Comment:
But we know that result transmission uses telephone, PPP, and a username and password, from Page 14 of the Hopkins report, quoted in Allegation #40. Therefore, it is quite possible that election central will have a LAN connection using Internet protocol, perhaps used to connect a modem bank with a single PC. This LAN may not be as vulnerable as the public Internet, but it is vulnerable to packet snooping and several other attacks, and must therefore be carefully secured. Furthermore, if an adversary can dial into the PPP host and await connections, Trojan horse applications on the voting system could communicate with the adversary using PPP without talking to the GEMS system at all. (DWG)
In its previous iteration under the Diebold logo, access to GEMS was already provided. Using a latent Trojan or latent dynamic code that isn’t detectable during certification or is added later and goes live during the election isn’t just possible with this system. Every door for it happening has been left open for over 22 years of election cycles.
Diebold (now Dominion) made public assurances that GEMS servers were/are not connected to networks despite the fact that some were. If GEMS has a pool of modems it is connected to the telephone system and security depends on how the modems are managed and who is managing them. Telephone networks are considered part of the internet. A GEMS server could be dialed and corrupt data directly. The modem bank can be tunneled through to gain access to the polling places and corrupt election machines directly. (DWG)
That fact alone along with Dominion Voting Systems specifically being the owner of this system is enough to decertify not just the elections Dominion contracted for, but the equipment itself, already long considered a threat to election security.
Intrusion into the General Election Management System (GEMS)
From its inception this election system used 3rd party add-ons. This includes Microsoft Windows OS and Microsoft Office software which depending on the definition used for can be loaded with other COTS (commercial off the shelf 3rd party software).
The problem found with Microsoft components (DWG) is the use of dynamic coding which can be used to change ballot results. From the beginning (1997), Bob Urosevich and Barry Herron insisted this was not subject to a source code audit.
The same Microsoft ACCESS program is shown above to swiftly and undetectably change the audit trail and results is what Diebold/ES&S and Diebold/Dominion demand protection for.
When Diebold (using Dominion’s current source code) was audited by Metamor for the FEC/NASED, they found the security of GEMS and the integrity of the audit trails were compromised because Microsoft Access can easily change that audit trail.
Diebold (now Dominion) convinced Metamor this wasn’t a problem for them because it was up to the customer to secure the election. In other words, they provided the means, training, and support for the crime, but cannot be held liable themselves.
According to (DWG’s report) this was despite the fact that Diebold (now Dominion) was aware that this security was being routinely breached: "Jane (I think it was Jane) did some fancy footwork on the .mdb file in Gaston [county Florida?] recently, I know our dealers do it. King County is famous for it. That's why we've never put a password on the file before." [See BlackBoxVoting on Diebold's Internal Memos or Alteration of Audit Log Access.]
While this is damning, it only gets worse. After Diebold’s source code was found on their website and examined, the code for the GEMS system used to manage elections and the Accutouch terminal was found. What became clear to (DWG) is the same code errors he pointed out half a decade earlier to Bob Urosevich and Barry Herron at Global Elections followed them to Diebold and was still in use.
This one point made Dr. Jones call for HYPERLINK "http://avirubin.com/vote.pdf" the decertification of the Diebold (Dominion) system directly after reading the John Hopkins University report.
Mail-in votes
In the (DWJ) report Diebold’s (now Dominion’s) assertion that security loopholes in their voting system is of no importance because customer safeguards prevent exposure.
But, despite supervision in a San Louis Obispo County election, the GEMS system used to accumulate absentee and mail-in ballots were connected to the Diebold FTP site live and the tally of votes was noted midway through the election. For this to be posted on GEMS is normal for any election. How did Diebold comes into possession of this data and post it on their website?
Sneakernet
Before the internet existed, sneakernet was the way hacking was done by loading floppy discs or smartcards into the victim's computer and adding malicious code or software.
We’ve all seen the videos of thumb drives handed off during the 2020 election. The fact they weren’t secured should have decertified the results. Smartcards and thumb drives were noted in (DWG)’s report as a major concern. In 2003, smartcards provided the interface for concern but these machines were not protected against inconspicuous devices like USB flash drives.
The locks on the machines themselves were noted to be so cheap it took no longer than 3 seconds to go past them. Gaining access took a team testing Diebold security 3 guesses to get the password and because Diebold (Dominion) uses the same login system-wide only one password gained supervisor credentials for every machine.
When Diebold/Dominion’s source code was read the researchers discovered a class of Security Key Cards that could be used to change default passwords.
Voting Machines
If it were the case that Diebold's machinery offered the possibility of a real audit of an election, in the same way that corporate accounting systems are supposed to be auditable, partisan bias on the part of the vendor would not be a problem, but this is not the case with direct-recording voting machines such as the Diebold AccuVote TS. Democrats want election machine firm thrown out, in the Port Clinton News Herald, August 27, 2003 and Voting machine controversy, in the Cleveland Plain Dealer, August 28.](DWG)
Universal Ballot Marking (BMDs)
According to Jennifer Cohn’s article on December 17, 2019 (NYRB), Universal use Ballot Marking Devices or BMDs function as electronic pens, mark your selections on paper on your behalf. Although vendors, election officials, and others often refer to this paper as a “paper ballot,” it differs from a traditional hand-marked paper ballot in that it is marked by a machine, which can be hacked without detection in a manual recount or audit. These pricey and unnecessary systems are sold by opaquely financed vendors who use donations and other gifts to entice election officials to buy them.
These scholars warn that even a robust manual audit, known as a Risk Limiting Audit, cannot detect whether a BMD-marked paper ballot has been hacked. BMDs instead put the burden on voters themselves to detect whether such ballots include fraudulent or erroneous machine marks or omissions—even though studies already show that many voters won’t notice.
Andrew Appel, an election security expert at Princeton University, said Georgia currently “has the least-secure voting machines now of any state” and is right to replace them.
But he said the touchscreen ballot-marking devices and optical scanners of the new system are easily hackable. And the system relies on voters to check their own paper ballots when research shows they do a poor job of it.
Printed-out ballots will include the text of voters’ choices, but scanning machines will read computerized bar codes to count ballots.-AJC
This means the only real audit trail existing today is in the hands of voters when they leave the polling station. The BMD ballot they cast is unreadable barcode. Their ballot can be changed at every point along the way at the voting machine to the GEMS system.
Patches and new software
"The ability to install patches or new software that wasn't certified has many risks, including the introduction of new bugs and more opportunities for tampering. It is even more risky if different patches can be installed at the last minute in particular jurisdictions," says David Dill, professor of computer science at Stanford University.
"This opens the possibility of customized tampering by people who know exactly which races they want to affect, or bugs that are even less likely to be caught because they only occur in a small number of locations," says Dill. "Of course, even if the certified code is frozen, it is easy to think of ways that undetectable back-doors could be installed in the software so that someone at the election site could choose the winner of the election." -Bev Harris
SAIC Conclusions on Dominion’s source code
The final paragraph of the executive summary of the SAIC report on the Diebold (now Dominion) system is pretty damning. The system is made to compromise. At the time six years had passed from the time the routes of compromise were discovered and Diebold’s system, now owned by Dominion is the same.
The system, as implemented in policy, procedure, and technology, is at high risk of compromise. Application of the listed mitigations will reduce the risk to the system. Any computerized voting system implemented using the present set of policies and procedures would require these same mitigations. [Page V, final paragraph.]
See Risk Assessment Report: Diebold Accuvote-TS Voting System and Processes, SAIC-6099-2003-261, Sept 2, 2003]
Furthermore, since SAIC examined the current certified version of the code, the version number of which was redacted in the body of the text but exposed in Appendix D as 4.3.1.5, this seriously damages Diebold's claims that the flaws reported in the Hopkins study were in old code that is not used in real elections.- (DWG)
With an over 20 year history of providing every means of election fraud possible, training people how to do it, making sure elections are hackable, can Dominion or ES&S claim innocence in 2020?
These election vendors have a history that’s mocked in Congress about the bribes they payout to the National Association of Secretaries of State (NASS) and other concerned parties.
Because the 2020 election season was Federal, every machine in every county that was hooked up to a modem was decertified for a federal election. In fact, the argument as shown above can be made for every system connected to any form of telephone systems as a backdoor to the internet and hackers.
Every state using the Dominion system ran decertified elections. The states elected to ignore federal election standards.
Can states that did not meet federal rules for elections after adding them into their own election certification requirements be considered legitimate participants in the 2020 election by choosing to ignore their own election standards?
The answer is no.
Subscribe to our evening newsletter to stay informed during these challenging times!!
I'd like to know why Pro V&V, the machine certification company for Georgia is never mentioned.
Dominion AND Smart Matic NED TO BE IN THE JUNK YARD BY NEXT Election!!!