Please Follow us on Gab, Parler, Minds
The conventional wisdom is social media giants like Twitter or Facebook are immune from lawsuits against them because of Section 230 provisions.
However, Section 230 immunity provides no protections for these companies if they are breaking the law by hiring or working with political terrorist groups taking direct or indirect instruction from foreign countries and attacking Americans or other civilian groups.
You’re about to read why and how the term terrorism applies. The obvious part is DNC has been involved in a scheme to purge America of Donald Trump’s supporters. The less obvious fact is the groups involved with the DNC tried to legally redefine cyberterrorism to protect the groups doing the purges, IO, strategic communication (media blitzes).
Because they did it in such a clumsy way, the legal manual they wrote which is used in US courts defines them as terrorists because their disruption of the social and political ecosphere in America is doing real damage as well as harming millions of people.
The natural remedy is massive class-action lawsuits against the social media companies working with companies targeting legally protected social groups, political groups, journalists, and the networks these connections exist on.
Under the law, terrorism is terrorism. It doesn’t matter what medium is employed. The act, whether it’s in cyber, social media, or at a physical location is defined by specific over-arching criteria.
The following is important because the group behind all that is going on in the US today developed international law guides to protect coup workers from liability to you. All of it was focused on US citizens from day one.
This group includes the DNC, Alexandra Chalupa’s Ukrainian Diaspora groups, the Atlantic Council, and the SCL-IOTA Global-Cambridge Analytica groups when they put this into action starting in 2014.
In a very real and legal sense, the perpetrators are soldiers on the battlefield which in this case is the internet. The tools they freely use against Americans are sold as real-world weapons internationally.
This becomes applicable to you on three counts.
· It describes what is happening to you and your communities as well as the remedy.
· It describes Social media cleansing as political terrorism once the terrorists are shown to be doing it for foreign and domestic political parties that declared you a political enemy.
· Because I caught this in early 2015, I was able to force a change that bounces the jurisdiction from a legally ambiguous international law of war (civilians) standing to the appropriate state jurisdictions in the updated Tallinn 2 document.
I accomplished this by showing IO leaders and Atlantic Council parties who wrote the Tallinn document providing their “volunteers” liability there was an ambiguous gap in their Tallinn 1 document. This left their workers (with foreign countries and domestic political parties) open to legal assassination because they were and are doing work for foreign militaries/Intel/ and governments against protected political and social groups including US citizens.
If their workers were provably working with foreign military (works on foreign government orders) or illegal combatants (terrorists pushing the agenda of foreign governments), the person dealing retribution was immune to international extradition based on their own document which is the gold-star document providing governments with legal advice in this area.
Tallinn 2 was published with the changes needed to provide legal standing for civilians in courts that didn’t exist before. The Atlantic Council, IO, and Intel Community writers reacted to the above by specifically stating civilians had no right to recourse in International Cyber Law. They took the additional step to define the jurisdiction civilian recourse would be found in are state and local courts.
This step is what makes the social media giants liable for the mass deplatforming. Cyber terrorism is defined under international law. State and local courts have much less experience with the concept but now the definition can reliably be made referring to the Tallinn document. Damages can be argued because terrorism in general is defined in state courts.
The addition of the Tallinn definitions is useful because these actors are working with foreign governments and as illegal combatants warring against fellow US citizens.
How does this apply to you? Scroll down to rule 26.9 where it says virtual online communities are off limits. Cyber is extended to attacks on virtual communities which result in their destruction. This includes deplatforming your followers which are your virtual community.
I’m going to take it out of the theoretical and put it in concrete terms after these definitions.
The Tallinn (1) Manual for International Law Applicable to Cyber Warfare defines cyber war as war. Cyber terrorism is terrorism. The medium doesn’t matter (conventional, nuclear, space, cyber, economic, etc) and the response can and should be in the real world.
Even though it is not a legally binding document, it is a practical resource for legal advisers on issues that up to now have mostly been tackled on ad hoc and case-by-case basis. “Tallinn Manual 2.0 is an invaluable tool for governmental lawyers responsible for providing legal advice in mainly two situations – first, when their state has become a victim of hostile cyber operations and would like to know its response options, and second, when the state is planning to engage in cyber operations, but needs to ensure that it does so in compliance with international law,” Vihul emphasises. Estonian World
The Black Letter Rules include: Rule 23.3 Cyber attacks against civilians is a war crime defined by rule 32.
Rule 26.7 -- The concept of "belonging to" defines whether you can be targeted or not. This rule defines civilians as off-limits unless they are "engaged" in real war duties. It includes undeclared relationships where behavior makes it clear which side a person is fighting for.
Rule 26.9 -- Virtual online communities and people expressing opinions do not qualify as combatants.
This includes Twitter, FaceBook, or other community. The damage isn’t just that a social profile is erased. People rely on social media for their business, communication with family, etc. The fact that virtual communities aren’t defined by geographical location doesn’t negate the concept of community or the damage done to it.
As an example, if someone has 5 Twitter followers in the UK, 26K in Germany, 200 in Australia, and 50K in the US, attacking or destroying any part of the community creates a liability to all of it.
Rule 30 -defines a cyber attack as a non-kinetic attack reasonably expected to cause damage or death to persons resulting from the attack. If the attacker mistakenly calls civilians lawful targets, the attack on civilians still occurred. It is a crime. This is an important consideration considering how interconnected the internet has made people.
Rule 31 -- Psy-Ops including leaflets, mass emails are not prohibited behavior.
Rule 33 -- If there is a doubt to the status of a person, that person is to be considered a civilian and not targetable.
Today, they are calling ISPs (Internet Service Providers) and demanding they take websites and news sites down by accusing site owners of terrorism or supporting terrorism. They call employers and accuse them of hiring terrorists to get people supporting Donald Trump or not supporting the DNC fired. This has been going on for over 20 years.
The following was about the people defending President Trump publically during the fake Russia gate accusations.

Rule 35.5 -- Gathering information for the military makes you a combatant
· Journalists are prohibited targets.
· Once an attack is made, the retribution is legal and does not necessarily need to be in kind. A cyber attack can be met with conventional weapons.
Rule 41 -- Means and Methods describes cyber weapons broadly as the means to carry out cyberwar by use, or intended use of cyber "munitions" designed to cause damage, destruction, or death to its targets. The breadth of the rule is required because of the wide array of possible attacks through cyber means.
The tools used on you today in social media had to be checked for International Traffic in Arms Regulations (ITAR) approval requirements for export use in Ukraine. ITAR governs the export of military munitions. In the US, they are free to use these same IO weapons on civilians.
Deplatforming, Social Media bans and President Trump’s 2nd Impeachment Hearing
Let’s start making this real through what Twitter and Facebook did to President Trump. The same groups that worked on his social media ban are busy building out the Capitol Hill sedition narrative. They are also the same groups identifying MAGA Trump supporters and getting them fired when they returned home from the January 6th rally.
Eliot Higgins and Bellingcat are hard at work identifying January 6th rally goers and custom building a narrative for Ilhan Omar’s impeachment designed to show Trump supporters were attempting to overthrow the US government. Higgins was smart enough to delete his tweet calling for the 25th Amendment to be invoked against Donald Trump.
Higgins and Bellingcat made it big doing the same kind of work in Ukraine and Syria. His business relies on the willingness of the US government to bring military personnel into areas his clients want.
Higgins and Bellingcat work with Ukrainian Information Operation’s partners InformNapalm, StopFake, and the SBU. Yesterday, Ukraine’s President Zelenskiy showed his colors finally by condemning Donald Trump and showing support for the impeachment hearing that’s about to begin.
President Donald Trump’s policies are bad for Bellingcat’s business.
Groups working with and around Bellingcat, the Atlantic Council, the DNC, and the Ukrainian Diaspora groups are the same groups making your social media profiles disappear deleting thousands of people from social media because of their politics or values.

This brings us to who’s doing this. In late 2019 Rand Corp wrote an article called Tools That Fight Disinformation Online highlighting some of the most potent tools being used today policing social media.
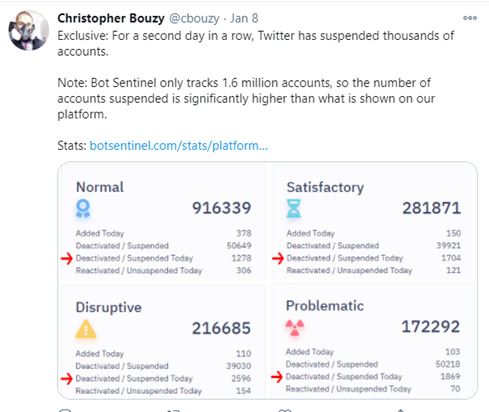
Bot Sentinel was third on that list. This app was designed by Christopher Bouzy with the express purpose of paring down social networks that supported Donald Trump.
There are literally hundreds of companies like this using political volunteers to tear social networks apart by researching where articles or posts go viral and banning those accounts. It’s not surprising most of these companies are supported by groups associated with the DNC.

Bouzy and his startup were hired by interested parties working with Ukraine, the Ukrainian Diaspora, the DNC, and the Atlantic Council. All of these entities are grouped together and the actors who fit the definition of political terrorists bounce in between groups depending on the project being forwarded.
How accurate are keyword-based political judgments used for social media bans? That’s all tools like this work on. If you understand anything about how our government works, his next tweet makes it clear BotSentinel which is used to ban hundreds of thousands of Trump supporters doesn’t work at all.
Its purpose is to provide an impartial looking cover for political purging.
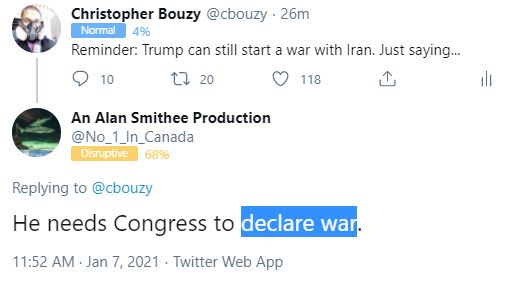
The account about to be banned from Twitter is making a simple point based on how the US government actually works. Bouzy and other companies working under Twitter feeding the recycle account make these decisions.
Is Bot Sentinel and companies like this part of a political terrorist scheme against Trump supporters? This is an important question. How much more biased can you be than relegating President Donald Trump to being a Putin controlled traitor when at the same time the Russian Ministry of Foreign Affairs isn’t labeled as Putin controlled?

A few years ago I looked under the hood and found out the decisions to ban social media accounts are made.
Bouzy’s magic depends on political operatives trolling accounts, geolocating, and doxing people. This information gets passed on to other groups that harass ISPs (Internet Service Providers) to take down related websites and new sites. This is literally all the magic used to decide social media bans.
The troll engages people and tries to get them to react. They add the profile to Bouzy’s or other companies’ systems turn them into Twitter and then the profiles are banned.
Because of the many different anti-Trump groups working together, the ties to domestic Information Operation companies, and foreign government support, it is clear cut political terrorism directed at specific social and political groupings.
When you look at the following, despite the screenshots, this is your story. Although yours may not have gone to this extreme, it is still your story. Look how coordinated the effort is to purge you not just out of social media but out of the political life of the nation.
During the process of exposing more of the DNC IO against Donald Trump, I came across the groups behind the purges.
After tying the DNC and Ukraine into the story, their reaction was trying to geo-locate me so I could be murdered. These groups started digging into my background to the point they were tweeting my wife’s 2005 Republican Party donations.
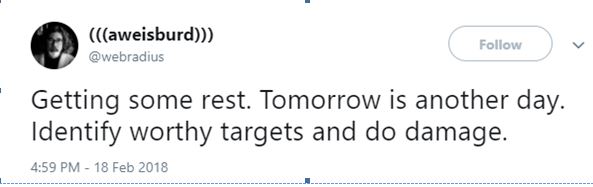
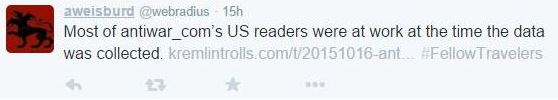
In the tweet below, K Johnson (works with the Atlantic Council and Bellingcat), Propornot (Ukraine, the DNC, and the Atlantic Council), Aaron Weisburd (FBI, DHS, NATO, CIA trainer working with the DNC and Clinton advisors), and David Hunt (Bot Sentinel), Chris Sampson (Tapstri Media, MSNBC InfoSec SEM, Intel Community, BotSentinel).
Bear in mind the groups these individuals are with are also in charge of fact-checking for Twitter, FaceBook, and Google. This screenshot shows part of their geolocation effort. This is being done to many Trump supporters today.

The Intel and InfoSec communities have been neck deep in this with the DNC from the beginning. When you read the following, understand this is the intellectual level of the people identifying you and working to take your jobs away even as this article is written.

After this, they brought in MSNBC InfoSec SEM Chris Sampson. Sampson and his partner Malcolm Nance have worked with Andrea and Alexandra Chalupa, the DNC, and the other groups listed above to destroy Donald Trump and his supporters since 2016.Sampson promptly blocked me so I looked at the conversation from a different social profile. He was still at it guiding his charge through the conversation in the background. They make their connection to each other by themselves.
This gives the term sockpuppet a new and intimate meaning. You can almost picture Hunt sitting on Sampson’s lap after this exchange.
This once again brings us back to their connection with Christopher Bouzy and his BotSentinel app ridding Twitter of Donald Trump and MAGA supporters. Chris Sampson’s partner is Malcolm Nance.
All of this adds up to specific Intel and political actors engaging protected social groups, civilians, and political groups to cause them harm. We’re not talking about trolling or arguing politics. These are Intel community professionals. From the 2016 election until now they’ve been building databases of people and getting rid of as many as they could all the way through the process.
This is the biggest question and unless answered Twitter gets to hide behind Section 230 protections.
The answer is yes. Twitter both knows and approves of this political and social terrorism against Trump supporters and Donald Trump. Coordinated attacks on social and political groups online is defined as an act of terrorism. That’s the DNC supported definition.
I brought my situation to Twitter. The screenshots above only begin to sample the proof I have as well as the very open threats these groups were sending directly at the time. Even with the screenshots and other evidence showing the definite connections all the way back to the DNC, this was Twitter Support’s response.
Death threats are protected speech. Stalking is a protected right.
I followed this up with a private message to @Jack. Again I provided the evidence to back up what I was saying.
Hi. I complained about private sector OSINT guys that are stalking me and your people said it was protected. Take a look.
Sep 4, 2018, 1:36 PM These people and others they work with are acting on behalf of the Atlantic Council and Ukraine. I am an American citizen journo that lives in the Donbass war zone. Now they are doing the same to my wife right down to political contributions for 2005.
Sep 4, 2018, 1:38 PM weisburd webradius puts people on lists and gets them killed. That's what he gets paid for. I'll show you the proof in his own words if you'd like. I've written a couple exposes about him and some of the others. He's proud of this.
Sep 4, 2018, 1:40 PM I don't think this is what you're about. At least I hope not. I can show you a lot of proof and how a lot of them work together if you like. I would like them banned or know why you won't. Again, I am writing about this. In the past, not on twitter, these groups have threatened me with torture (Ukrainian SBU), and this makes the 4th threatening gesture. I'm not waiting around this time. If you don't answer, that'll be your part in the article.
Sep 4, 2018, 1:44 PM The best thing that can happen is these guys are regulated by Congress. Attacks on Americans by private parties working for foreign governments can't be tolerated no matter how they shape up. I hope America can get through this quickly. Who'da thunk it?'
Sep 4, 2018, 1:46 PM I'll be writing the article for thursday publication I hope. this is what their bosses are mad about. washingtonsblog.com/2018/09/beyond…
Sep 4, 2018, 1:48 PM I'm putting the article off for a few more days. I certainly hope to get a statement from you.
Sep 7, 2018, 11:17 AM Thanks for your response. It's funny, the same guys are now trolling an article I "am going to" write, and I don't have an issue with this. That's part of the terrain. But, when they are working their asses off to geolocate me for harm, you don't have an issue with that. Good enough..
Sep 19, 2018, 7:25 AM Sent You can no longer send messages to this person. Learn more
Jack’s response is essentially a receipt of the message. He read it. He understood it. He didn’t want any more messages.
Because this has been addressed to Twitter and Jack Dorsey and they responded, they can’t hide behind Section 230 anymore.
What this means for you is massive class-action lawsuits not only against Twitter and other social media giants, but Apple and Amazon just jumped into the game openly. Just the few people listed above are a direct line to the DNC they work with. The Atlantic Council is another. Alexandra and Andrea Chalupa open up the Ukrainian Congressional Committee of America (UCCA) and Ukrainian World Congress (UWC) who footed the bill to get all this started.
Behind those two groups, there are around 140+- US Congressmen and Senators willfully supporting this the entire time. Intel Community, IO, and Strategic communication companies are doing a lot of the leg work.
This means by organizing a class-action lawsuit, you’re not only taking a stand for yourself and Donald Trump, you are literally draining the swamp trying to suck the Trump presidency under today.
When they said “Back of the bus!” Rosa Parks said no. Be Rosa Parks. She was an American hero.
Subscribe to our evening newsletter to stay informed during these challenging times!!